

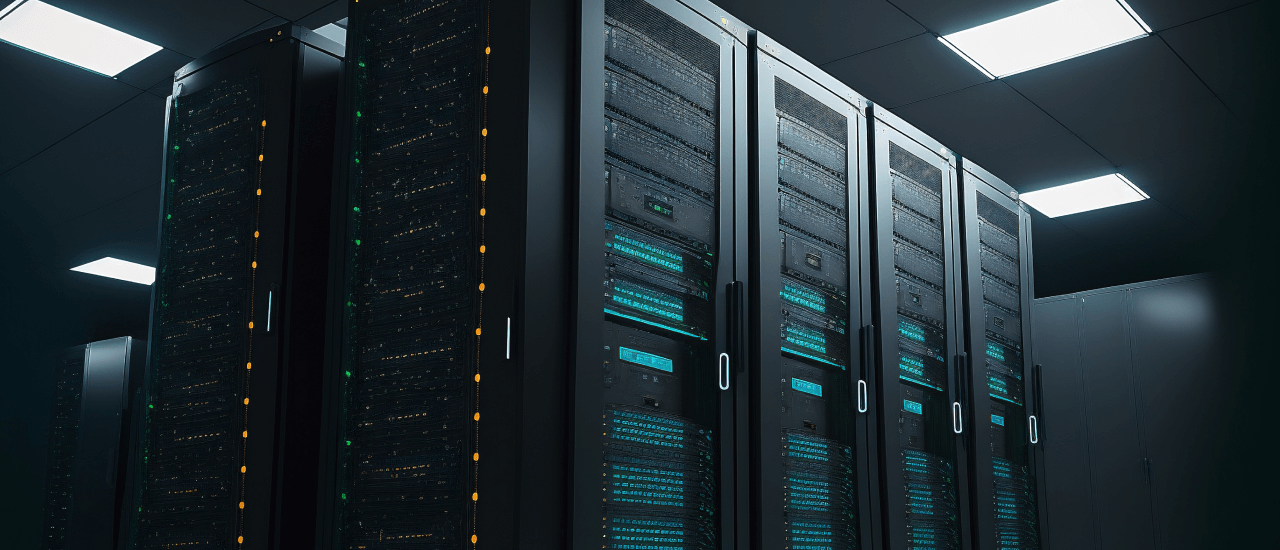
TechForing offers a comprehensive approach to penetration testing. We perform system breaches with expert pen testers, leveraging the same tools and methods malicious hackers use. We do it to make the test as realistic as possible. We provide penetration testing for both internally and externally accessible infrastructure and services. This includes web apps, network hosts, hardware, mobile devices, and even humans, through our physical testing and social engineering. We perform penetration testing as one-time or recurring services for maximum protection
industries we serve
Any business, no matter how large or small, should undertake penetration testing if the business deals with sensitive or valuable customer information. In fact, recent statistics have shown that smaller companies are increasingly becoming targets for cyber criminals simply because their IT security is weaker. Some of the industrial sectors that require penetration testing include:

Retail

Transport

Education

Banking

Healthcare

Hospitality

Information Technology
PEN Testing that Leaves No Stones Unturned
We provide penetration testing for many targets–both externally and internally accessible infrastructure and services. This includes web applications, networks, hardware, mobile devices or even humans, through our physical testing.
We can deliver our services as a one-time service or on a recurring service for maximum protection.
Our pen testers work in a streamlined series of five phases listed below. When put together, these phases form a comprehensive approach for completing a successful penetration test.

Before starting the pen test, our pen testers will meet with the clients to define and set the goals of the test. This will help us scope and execute the operation properly. We'll learn about the tests you'll be running, who will be aware of the tests in your company, how much information and access our pen testers will have from the start, along with some other crucial details. After setting up the parameters, we will start gathering information about the target. We will source our information from public and private sources to form our attack strategy. Our sources include OSINT, social engineering, non-intrusive network scanning, etc. Gathering this information helps our pen testers map out the client's attack surface and vulnerabilities.


In this phase, we scan your network both internally and externally to discover various vulnerabilities that exist. Our pen testers use various pen testing tools and network penetration testing to examine the target system or website for weaknesses. These weaknesses can include open-source vulnerabilities, application security vulnerabilities, open services, etc.


After learning about the target's weaknesses, pen testers start infiltrating the environment, exploiting as many vulnerabilities as possible. These security breaches demonstrate just how deep into the system an attacker can go. Exploits usually include escalating privileges, intercepting traffic, stealing data, etc.

After completing the tests, we compile the results into a report detailing the security risks, the vulnerabilities that were exploited, the critical data that was accessed, and the amount of time we were able to stay in the system undetected. Our penetration testers include every step of the process in detail, highlighting the pen tools and methods used to successfully penetrate the system. We also include evidence of our discovery process and remediation recommendations. We rate vulnerabilities as critical, medium, or low, followed by an overall security rating for your business, enabling your security teams to assess and fix the most crucial issues.


After learning about the target's weaknesses, pen testers start infiltrating the environment, exploiting as many vulnerabilities as possible. These security breaches demonstrate just how deep into the system an attacker can go. Exploits usually include escalating privileges, intercepting traffic, stealing data, etc.

After completing the tests, we compile the results into a report detailing the security risks, the vulnerabilities that were exploited, the critical data that was accessed, and the amount of time we were able to stay in the system undetected. Our penetration testers include every step of the process in detail, highlighting the pen tools and methods used to successfully penetrate the system. We also include evidence of our discovery process and remediation recommendations. We rate vulnerabilities as critical, medium, or low, followed by an overall security rating for your business, enabling your security teams to assess and fix the most crucial issues.

All-In-One Service : All-In-One Service We provide your company with mitigation steps and remediation recommendations to address all the vulnerabilities we identify during our testing. Our stand-out feature is a combination of a world-class data security team and highly advanced automated testing performed by automated tools, all under one roof.
Experienced Hands On Deck : Experienced Hands On Deck Our years of experience in infiltrating the networks of some of the world's greatest adversaries helped us develop advanced techniques to penetrate target networks. Our advanced techniques go far beyond conventional automated scanners and leverage the highly skilled human factor.
Expertise In Proceedings: Expertise In Proceedings We will expose your entire network and infrastructure's vulnerabilities. We will hack your security controls before hackers do, ensuring complete security for you and your customers. Our security assessment will pinpoint as many vulnerabilities as possible in our tests. Don't let the uncertainty of an insecure network worry you a day longer. Contact us today and we will help you solve the configuration issues of your IT infrastructure.


Our website needed a risk assessment. TechForing Engineers are a pro in that. They did everything needed to get the job done. Guys are content and I got my piece of mind. Thanks, TechForing.
Schedule a meeting with our team
Secure nowimportant resources

Cryptojacking refers to the unauthorized use of a person’s or group’s processing power to mine cryptocurrencies like Bitcoin and Ethereum.

Credit card hacks claim hundreds of thousands of victims each year. In this article, we discuss some of the most …
It is essential to design a secure office network that maintains sufficient security in order to prevent any loss or …
